These steps can help strengthen your defences.
Counting Down…
10. Patch .. Update.. Upgrade.. and then Risen & Repeat !
This goes without saying… You need to keep up with your patches. There are tons of Zero Days exploits coming out and yet some of them are not patched right away since they are Zero day but you can still protect yourself from the ones they patched up. There is no excuse of not updating your windows and other software when it comes to patching. Yes you need to update all your other softwares as well since they can be the weakest point in your network. You can have Windows OS patched up to latest version however, a vulnerability found in WinRar or any other software can compromise your whole network.
It also goes without saying that you should not be using any pirated softwares as 99% of the time they have some kind of backdoors for hackers to take over your machine. They might not get triggered right away but they can be silently waiting for commands from hacker to activate and steal your data or to make your computer a zombie client which can be used to DDoS attack – Distributed Denial of Service other companies just for giggles for the hacker. Below is an illustration of an DDoS attack. You don’t what’s inside the code for cracks/patches…

9. Antivirus and Network monitoring
Make sure you have proper Anti-Virus software and that it is fully functional and updating properly. First thing any virus software does is deactivate your protections. You need to make sure you keep an eye on your Anti-Virus software from time to time. If it active scanning has been stopped or its not even running then that means your security has been compromised.
Also note that mayne Anti-Virus just does not look for other types of malicious softwares i.e. malware softwares or adware software which are pesky little things and those needs to be cleaned up by professional software which look out for these kind of pesky software. One that comes to mind is MalwareBytes it has a very good reputation around the global for cleaning up infected systems.
If your budget permits you should also deploy SIEM Security Information & Event Management solutions.
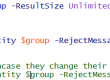
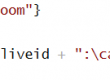
However, if you are small or midsize company and you have a tight budget you can deploy PowerShell scripts to alert you when some abnormality activity has been found and these can be done via filtering your Events Logs from Active Directory Server.
You might have seen some of the SIEM features being triggered by Gmail, Dropbox, Online Banking and many other web based solutions when you try to log into their services from an unknown location. These events basically knows that you have been logging into your services via specific IP + Location and when you go on vocation for example your Public IP and Location of that IP changes with it so that in-turn triggers an event and shoots out and Email to you and their security team for follow-up.
8. Email Filtering (Scam, Phishing, virus attachments)
As you might have already read there has been rise in Phishing attacks on companies and government offices. These CyberAttacker use techniques which utilizes social media to target an attack on a specific company. Since these attack are usually targeted, the success rate of these are very high unless you have well educated employees who are trained to look out for these attacks. Some of these attacks can be so simple that an employee might not even think twice.
For example, an employee can get an email from his manager asking him to buy couple of gift cards since he got stuck in the meeting with CEO and that the CEO wants to give out Gift Cards to his direct reports for amazing work and a P.S note would say since I won’t be coming back to my desk can you just send me the codes for those Gift Cards via email. Another, attack I have seen during our chat with clients is changing the Payroll of employee to another bank. Request comes in as an employee stating that he/she has change banked and that Payroll needs to update the payment using the below Direct Deposit form provided.
This is why deploying solutions to catch these nasty attacks before they reach your employees is very important. This way you are protecting your employees and your data from breach.
If you are using cloud solutions these options are available by default however, out of the box solutions even on Office 365 is not sufficient unless until you tweak them to your business setup. You can also make specific rules to catch a known phishing attack that way similar attacks cannot be used again on your company. Since at start hackers only try specific user however, when it does not work they start to email every email they find for a company and start targeting them too.
7. Plan out for Types of security event
So you got hit! now what? well either you can run around the office like a headless chicken or have actual plan on how you going to isolate and recuperate. There is nothing wrong with getting hit by an attack, however how you handle it has a lot to do with how things will go for you.
- Identify breach/attack
Successfully identifying your attack can help fight it and stop it from spreading. if one of your employee came to you and said oh I think I have accidently clicks on a phishing email and provided my username and password. Then instead of educating the user on his mistakes you should take steps to first address the issue by deactivating his account and doing audit trail and running anti-virus and malware scanning on his/her pc.
You also need to be cognizant documents exposed via cloud services i.e. if your company utilizes Office 365 then make sure all your SharePoint documents are protected and the said user has not uploaded any document files with a macro which could spread viruses to other employees.
- Detach & Quarantine
If attack has installed some malicious software or you believe it might have then disconnect it from network and run full scan on it. If you have a possibility of nuking the system I would suggest go for it. However, make sure your user has all important document backed up before you nuke it.
6. Backup and then back up to backup that backup.
Yes that sounds funny but dont mess around with backup. Only way you can be protected from ransomware is to have consistent backup solution. Since, backup eats a lot of space it is very crucial to identity your important data and have specific policy to perform backup on a higher retention then your normal data. You can even have more frequencies on your important data i.e backup it up 3 times a day one before the workday starts, one by the lunch hour and one end of the day. I know some of you might just said backup during lunch hour? is he crazy.. no you can have backup done via VSS Shadow copies and only cost for that might be little slowless on the system but hey its cost of having a backup when you need it. These days ransomware are going after backup solutions and some of them basically deletes your checkpoint on virtual machines and even deleting your backups. So to counter that you should also protect your backup from deletion which can be done by many ways. I will let you figure that one out however, you can leave a comment and maybe we can discuss it here 🙂
5. Whats what on Network?
Knowing your weak points are very important. No I am not talking about job interview question I am talking about company network. Know what can connect to your network and how can you remove it from network when some malicious intent is found via user.
Unless until you have deployed state of the art solutions at your company there are couple of weak points on any company networks. They are usually related to WiFi and BYOD devices or rogue devices on network.
Your employees can register their own mobile devices to WiFi and create issues if they have malicious software on their phone or they can just bring their personal laptop in which has millions of viruses since they love to download pirate softwares. These issues are very hard to fight against unless you have proper backend security which can prevent users from doing these unauthorized actions.
For preventing users from bringing in personal laptop you can implement 802.1x security which basically makes them authenticate before they can have access to the network. However, your switches should be capable of doing 802.1x authentication.
For preventing users from connecting to your corporate WiFi which gives them access to everything then using device based certification for SSID would make sense however, you will need to deploy device certificates to his/her device.
4. Switch based (acl) Access control list
Another security implementation can be done is ACLs on switch level. This can be done by splitting your VLANs to Servers, Computers, WiFI and guest WiFi. This way you can create specific access rules for each of these Vlans. One example could be that normal Computer can only talk to specific servers via specific ports. This way you can blocking all ports going to your server. You can also lock it down more to have only RDP access enabled for your IT Admin team etc..
For WiFi you can lock your guest WiFi SSID to just internet traffic and don’t provide any access to your internal network. This way even if they manage to break in due to bad security or someone giving out guest WiFi password to someone malicious they would only be able to go on internet from there.
3. User Education
You need to train your employees for attacks and maybe send out mass email when you find new type of attack addressed to your company. This way information is provided to end user and they are aware of these attacks and avoid. They need to recognise suspicious activity and flag it to your IT department. These activity can not only come from email but also from phone itself.
A lot of successful hacks has been done via phone as well where threat actor impersonate someone else to either get more information about the company or even get username and password. Once they have someone’s credential they can go next level by using credibility of that compromised user and attack payroll or accounts department.
2. Reset Default passwords
Never leave default passwords on any device… enough said!
1. Block USB Drives and Removable Media using Group Policy
Yes!! you heard me. Block those removal devices. It will save you tons of headache. You can even blame it on DLP when you do implement this setting.
There are ways to block it from GPO for all users or just specific ones via security group. For example, if you don’t trust your domain admins that much you can block them from using USB. However, since they are domain admin they can go and change the policy too which could be funny but if you do it right audit trail will catch the naughty admin.
Hope you enjoyed reading our article. Feel free to check out our services.